1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
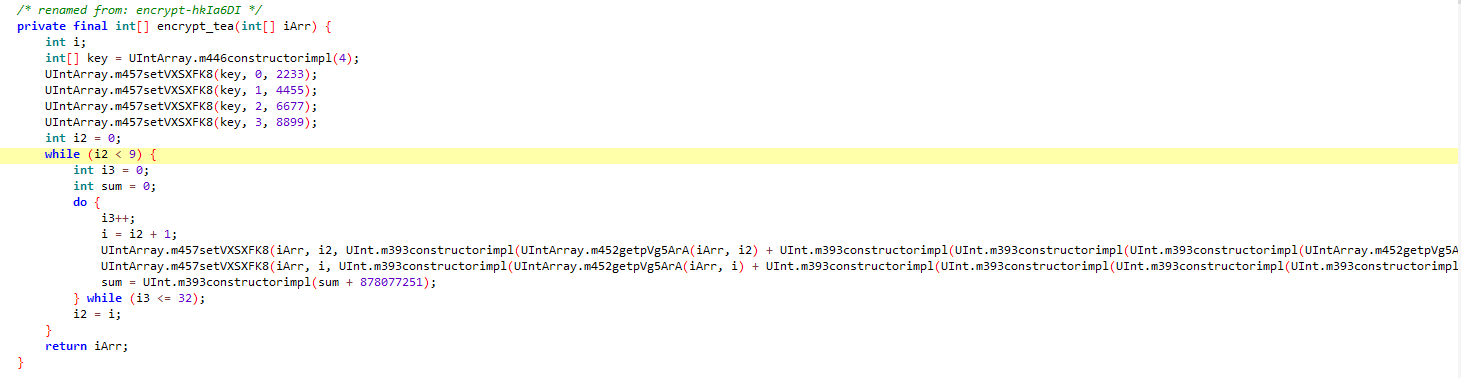
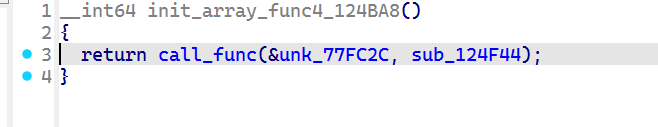
| #include <iostream>
#include <stdint.h>
using namespace std;
void decipher(unsigned int num_rounds, uint32_t v[2], uint32_t const key[4]) {
unsigned int i;
uint32_t v0 = v[0], v1 = v[1], delta = 878077251, sum = delta*num_rounds;
for (i = 0; i < num_rounds; i++) {
sum -= delta;
v1 -= (((v0 << 4) ^ (v0 >> 5)) + v0) ^ (sum + (key[(sum >> 11) & 3]));
v0 -= ((((v1 << 4) ^ (v1 >> 5)) + v1) ^ (sum + key[sum & 3])) ^ sum;
}
v[0] = v0; v[1] = v1;
}
int main() {
uint32_t v[] = { 637666042 ,457511012 ,-2038734351 ,578827205 ,-245529892 ,-1652281167 ,435335655,733644188,705177885 ,-596608744 };
uint32_t key[] = { 2233,4455,6677,8899 };
for (int i = 8; i >=0; i--) {
decipher(33, v+i, key);
}
for (int i = 0; i < 40; i++) {
char tmp = *((char*)v + i);
cout << tmp;
}
}
|


/image3.png)